Electronic data is your organization’s lifeblood & protecting it is critical to your success. TDI has the expertise to help you develop risk management strategies for stewardship of your data assets.
The explosion in computer interconnectivity, most notably in the growth in Internet usage, has revolutionized the way that governments and the private sector conduct business. Electronic data is the lifeblood of your businesses, so protecting that data is critical.
We are fully prepared to support the risk management process to help you assess risks and then manage them, dynamically and continuously. This is a natural extension to the holistic approach of establishing an organization-wide information security program.
TDI’s approach to risk management stems from years of experience implementing best-practice solutions in the government and private sectors where security of your data is an integral and high priority component of the solution life cycle, not an afterthought. Our approach emphasizes confidentiality, integrity, availability, authentication, and non-repudiation while addressing the need to scale our capabilities to varying degrees of system complexity. To meet this need we developed a strategy that closely adheres to NIST’s Risk Management Framework (RMF) and relies on a lifecycle approach for other security services.
Our approach demonstrates the application of security controls and technologies that are governed by the RMF to meet the requirements imposed through regulation, policies and standards to ensure security risks are clearly communicated, mitigated, and managed to protect and ensure resilience of your systems, information and business processes.
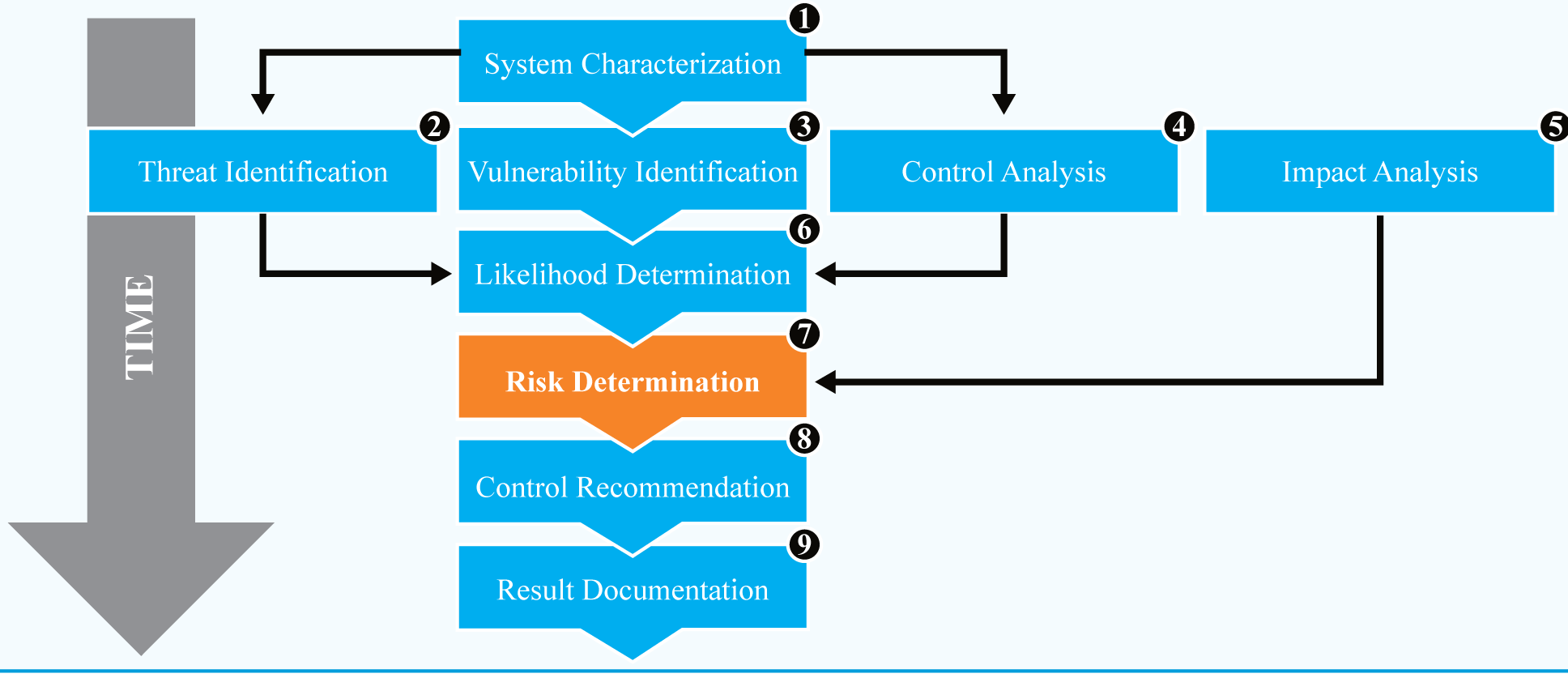
To begin with, TDI can perform a risk assessment of your organization’s IT network, system, or application to provide a comprehensive examination of the security measures and controls, of both a technical and practical nature, employed by your organization. We will gather information about vulnerabilities through interviews, site visits, review of documentation, and on-site observation of procedures. TDI’s risk assessments reveal pertinent information about the threats, vulnerabilities, and risks that exist. Each identified risk receives an associated qualitative form of measurement to evaluate it on a relative scale. Our risk assessment provides the foundation for an organization to make informed decisions about which controls and weaknesses require focus and potentially resources which then is integrated into the overall risk management process. Our typical risk assessment looks much like the following:
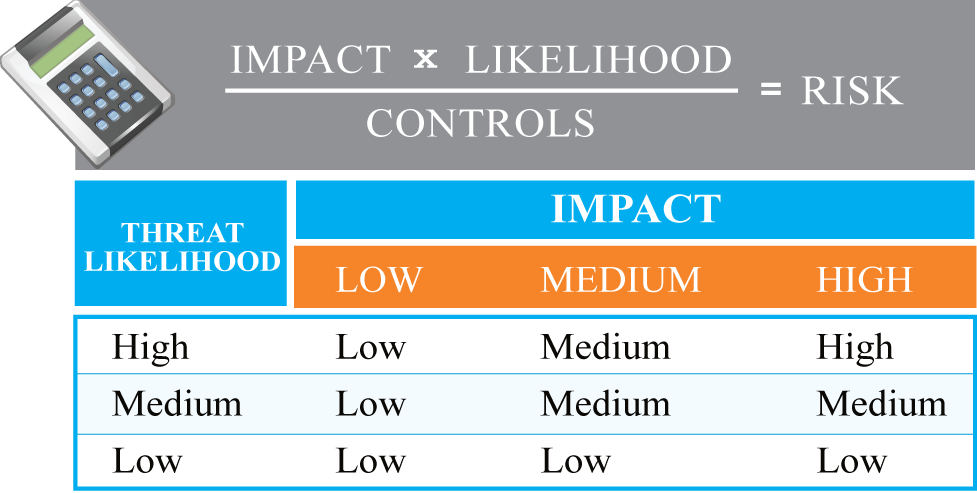
TDI has the experience and knowledge to help your organization conduct risk assessments to create appropriate strategies and controls for stewardship of your information assets. Our methods are disciplined and often rely on mathematically sound practices. For example, our calculation of risk is quantitative as in the following:
Let us work with you to determine your cybersecurity risk posture, assess your current risks, and put in place a framework to manage risk going forward.

